Regardless of industry, most companies have client and company data, a web presence-and, if regulated, many cybersecurity requirements to meet. So they inevitably arrive at the challenging question of whether they need a Chief Information Security Officer (CISO).
CISOs Play a Crucial Role
The simple answer is yes, companies need a CISO on board, and many regulated companies are required by law to have one. The protection of critical data is paramount today. And with the COVID-related surge in remote working, cybersecurity has become an even bigger concern.
Now more than ever, senior management is accountable for protecting their companies from data breaches that could impact their reputation, regulatory standing, market value, and customer and shareholder confidence. Leading practice is to assign a CISO with specific responsibility to do just that. Or, “virtual CISOs” (vCISOs) are increasingly hired by smaller companies to perform the same role as a CISO without being on staff.
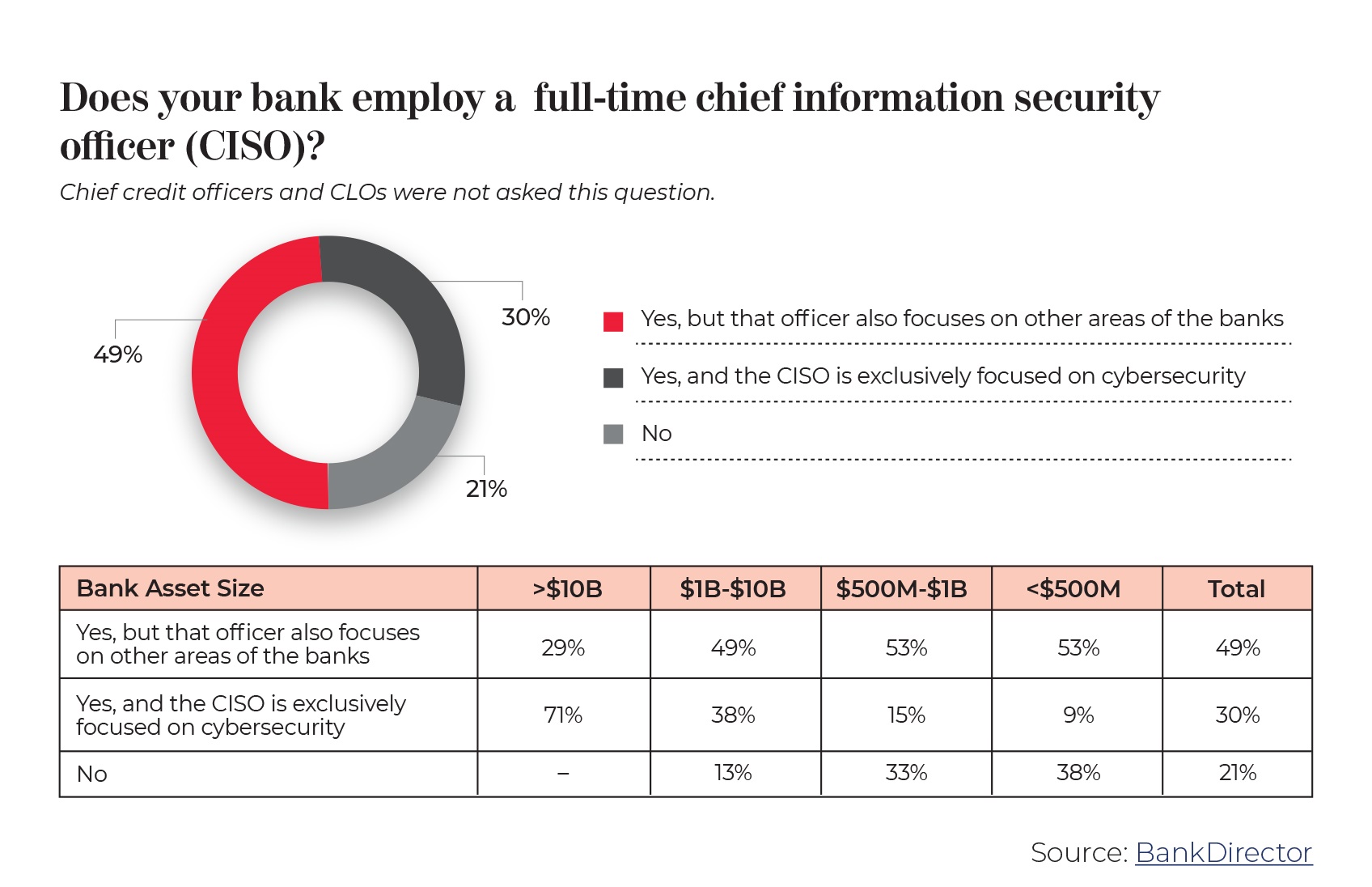
In the financial services industry, progress in this direction is mixed. Over one in five banks responding to BankDirector’s 2020 Risk Survey said they did not have a CISO; 30% had hired a CISO exclusively for cybersecurity; and 49% had someone performing multiple roles, including the CISO function. These numbers have not drastically changed since last year, even though this highly reguIated industry faces growing cyber risk and some of the toughest rules on cybersecurity.
Some companies struggle to decide: CISO or no CISO? Often, senior leadership and board members question the need, believing that the IT department can handle cybersecurity. This can be a challenge for internal advocates of the cybersecurity function. How do you persuade senior leadership that it is beneficial to the company to have this dedicated role with specific responsibilities? A big part of the answer is found in the following examples of regulators’ expectations for the cybersecurity function in the health and financial sectors.
HIPAA Security Rule
The Health Insurance Portability and Accountability Act of l 996 (HIPAA) includes a Security Rule, requiring all covered entities and business associates in the healthcare industry to appoint a “security officiaI” with the responsibility for administrative, physical, and technical safeguards to protect electronic personal healthcare information. While more than one individual may be given specific security responsibilities, especially within a large organization, the rule specifies that a single individual must have the final, overall responsibility.
Many in the healthcare industry have found it challenging to find a CISO who can perform at this level. However, the vast and growing amounts of personal information in their databases require strong security programs and related controls, managed by competent CISOs.
NYSDFS Regulation
Companies reguIated by the New York State Department of Financial Services (NYSDFS) must comply with Part 500 of Title 23 of the Official Compilation of Codes, Rules, and Regulations of the State of New York, which took effect in March 2017. In particular, Section 500.04: Chief Information Security Officer indicates that “each covered entity shall designate a qualified individual responsible for overseeing and implementing the covered entity’s cybersecurity program and enforcing its cybersecurity policy (for purposes of this part, ‘Chief Information Security Officer’ or ‘CISO’) ” The NYSDFS says that the CISO may be employed by the covered entity, one of its affiliates, or a third-party service provider.
Companies that do not comply with Section 500.04 could be fined significantly by the NYSDFS-and their fines could increase if there is a data breach while no dedicated CISO or vCISO is in place.
FFIEC Requirement
Guidance from the Federal Financial Institutions Examination Council (FFIEC) includes the following federal requirement from the Management Booklet, Section I.A.2(c): Chief Information Security Officer: “The Chief Information Security Officer (CISO) is responsible for overseeing and reporting on the management and mitigation of information security risks across the institution and should be held accountable for the resuIts of this oversight and reporting.”
The FFIEC also indicates that the CISO’s job has evolved over time from a technical function to a more strategic role within the organization. The CISO or vCISO is expected to be more of a risk manager than an IT manager.
CISO Skills and Reporting Structure
Whatever the regulation, it is best not to have the CISO or vCISO reporting to the IT department, to avoid any potential conflicts, and to ensure some level of independence and accountability. It’s up to the senior management to ensure that the reporting structure of the cybersecurity function will meet the expectations of regulators and external auditors. A company’s size and business operations will certainly play a role in that structure.
The basic skills needed today from a CISO are risk management, budgeting,and a good understanding of general compliance, audit, and technology operations. Another desirable skill is the ability to translate complex technical and security information into terms that C-suite executives and board members can understand i n order to make key decisions. The ideal CISO should have some prior experience in many of the information security fields (e.g., networking, access management, monitoring and reporting), but does not necessarily need to be a subject matter expert in all of them.
The CISO has to be a security champion and relay that message throughout the company to build alliances with the business and technology teams. Information security is all too often viewed as a roadblock to making progress and meeting deadlines. As such, it needs to be sold to leadership as an integral part of business projects to keep the company safe. Building bridges instead of walls within the company will make the CISO’s work more effective.
Whether or not senior management decides to hire a CISO/vCISO, they must take ownership of the decision. Ultimately, they will be held accountable for both the hiring decision and for establishing a reporting structure that wiII allow the individual to succeed. If hiring a vCISO instead of a full-time employee, there could be some scrutiny by regulators or internal and external auditors. However, management can address any such concerns by demonstrating that the vCISO is well managed and has both the independence and reporting structure to perform effectively.
